PCI DSS 4.0 has evolved the Standard's Multifactor Authentication (MFA) requirements. The updated Standard now calls for MFA for all access into the Cardholder Data Environment (CDE) as well as updating specifications on the functionality of the MFA solution.
These new MFA requirements are considered best practice until March 31st, 2025, after which they must be fully implemented for an entity that is maintaining compliance with PCI DSS and if the specific controls for multifactor authentication apply to their environment.
Account hacking and data breaches involving the use of lost or stolen credentials are the most common security threats that users encounter in cyberspace, involved in over 80% of breaches. It is no surprise that these additional control measures have been introduced into the PCI DSS.
MFA for all remote network access from outside the corporate network environment by users, administrators, and third parties has been a requirement since the advent of PCI DSS, and upon release of PCI DSS 3.2, it was also required for all non-console administrative access into the CDE.
The new all access MFA requirement applies for all personnel access into the CDE, including access by employees, contractors or consultants, vendors and other third parties, with the exception of user accounts that only access one card number at a time to facilitate a payment transaction, consumer (cardholder) accounts and application or system accounts performing automated functions. The requirement applies for all access to all types of systems and devices and applications, whether cloud, hosted or on-premise.
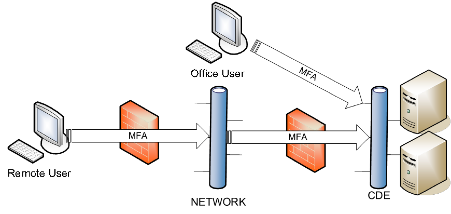
It is also worth noting that this is a new requirement on top of the existing MFA requirements. If you have remote users already using MFA to access the corporate network, this adds a second level of MFA. As is illustrated below: the remote user first needs to authenticate using Multifactor Authentication to connect to the corporate network, and then authenticate for a second time using MFA when connecting to the CDE networks or systems.
If your organization has implemented a cloud solution, where all or part of your CDE resides in the cloud, this future-dated requirement may require further implementation as it is likely that all access into the CDE would be defined as remote access and authenticating twice using MFA will be required.
Authentication is the method by which the individual proves that they are who they claim to be by providing at least one authentication factor that corresponds to the identifier (unique ID, userID or logon) they have provided. The factor could be something they are, something they know or something they have. When it comes to MFA solutions, a minimum of two different types of authentication factors are required to confirm the validity of the individual's claimed identity.
A common statistic cited to demonstrate the value of implementing MFA is Microsoft's 2019 finding that 'MFA can block 99.9% of account compromise attacks. In more recent times, however, it has been recognised that while MFA does significantly decrease the risk related to lost or stolen credentials, attackers have worked out ways to bypass or compromise MFA. PCI DSS 4.0 addresses these threats with its update to MFA implementation requirements.
For the actual authentication process, the MFA implementation has to be set up so that the success of all authentication factors presented is required before access is granted. This means that access is granted, or denied, only after both factors have been processed. If authentication factors are submitted and processed individually, unauthorised persons may be able to deduce the validity of each factor; reducing the authentication process to a two-step, single-factor authentication process.
The updated MFA specifications also require that the MFA solution is not susceptible to replay attacks, meaning it is not possible for an attacker to successfully gain access by recording and replaying a previous MFA authentication, and cannot be bypassed by any users without authorisation. MFA bypass could include scenarios where users are able to grant themselves persistent access, for example by making use of 'remember me features that negate the user's need to remember and enter their password (first factor). Summary and Next steps:
- Create a project plan to ensure that your MFA controls are updated by March 31, 2025 at the latest.
- Review your current MFA solution and assess if it can be extended to handle all users with access to the CDE.
- Ensure you include all CDE network, system and application access (including web-based access).
- If you allow for remote access, ensure the environment is set up to require MFA twice: once for any remote access to networks with access to the CDE, and MFA again when connecting to the CDE.
- Ensure that your MFA solution is set up to meet the updated implementation specifications ensuring it is resistant to attack, cannot be bypassed, and access replies are not given until all factors have been processed.
References:
Standard - https://docs-prv.pcisecuritystandards.org/PCI%20DSS/Standard/PCI-DSS-v4_0.pdf
FAQ - https://www.pcisecuritystandards.org/faq/articles/Frequently_Asked_Question/Is-two-step-authentication-the-same-as-two-factor-or-multi-factor-authentication/
Guidance - https://docs-prv.pcisecuritystandards.org/Guidance%20Document/Authentication/Multi-Factor-Authentication-Guidance-v1.pdf
Related Blogs
Stay up-to-date on the latest happenings in Cybersecurity and PCI Compliance.

AI-Enabled MDR: What Distributed Enterprises Need to Know Before Buying the Hype





.png)