MANAGED SECURITY SERVICES
Cybersecurity for Distributed Enterprises
Whether you’re managing 10 or 10,000 locations, we keep every site protected, connected, and driving revenue.
That's Business Uninterrupted.
.webp)
Your trusted cybersecurity defense partner.
300+
corporate brands under management.
50,000+
locations managed.
10,000+
franchise owners in our network.
98%
customer retention.
350,000+
network and security devices installed.














Our unbeatable capabilities.
Cybersecurity for distributed enterprises.
Built to keeping you running.
Managed firewalls, SIEM, IDS/IPS, endpoint protection, vulnerability management, and MDR. Integrated by design. Fewer gaps for attackers. Less complexity for your team.
AI-powered Asgard Platform®.
One view. One partner. Built for scale.
AI-powered cybersecurity, connectivity, and compliance visibility in a single pane of glass. Built to manage 10 to 10,000 locations without adding complexity.
Expert-led service.
Hands-on. Always-on.
Customers describe us as innovative, reliable, and secure. 24x7 expert support, with you from day one.
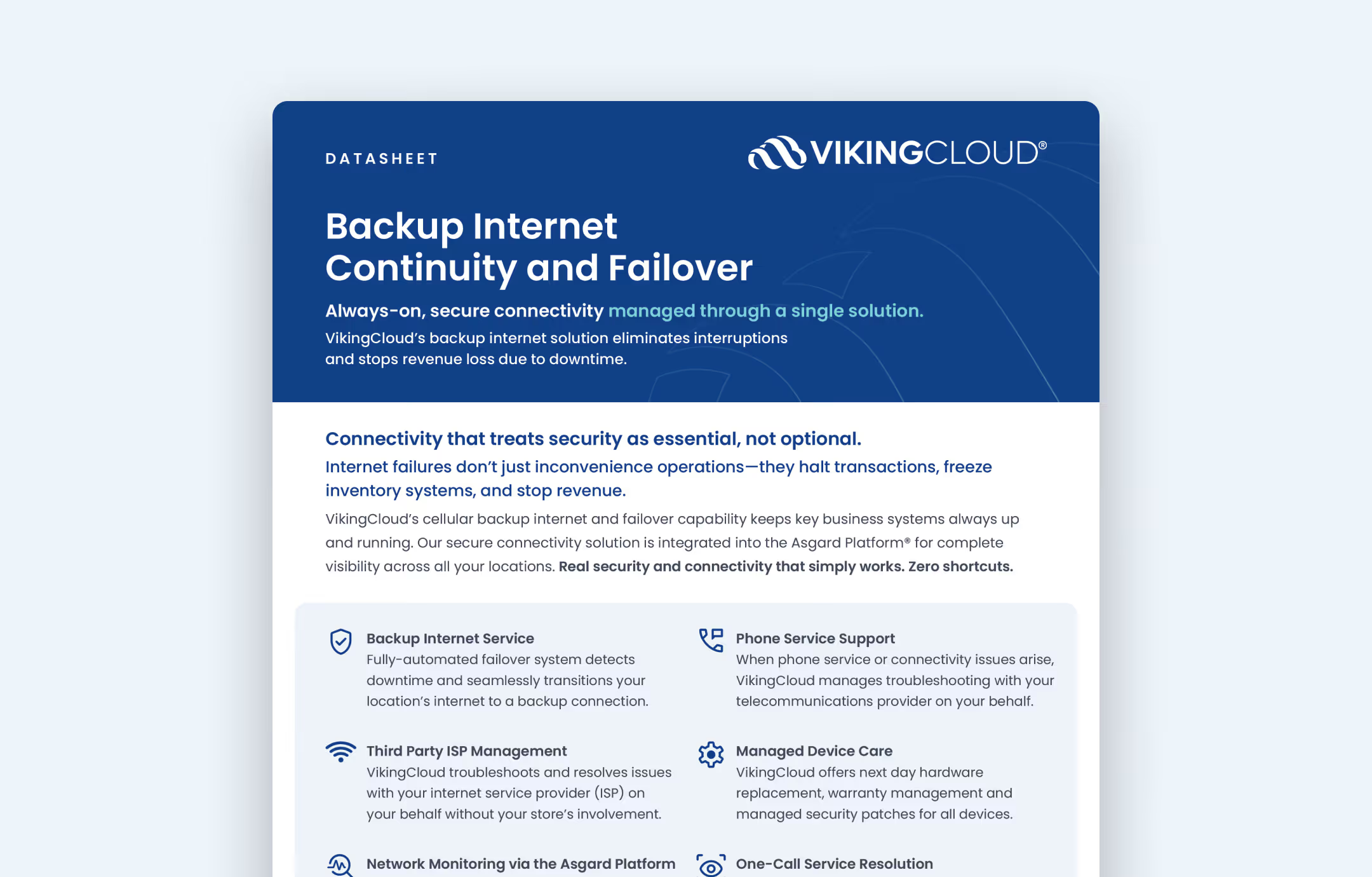
Always-on, secure connectivity.
Never miss a transaction.
Managed broadband, 5G, and cellular failover, integrated into the Asgard Platform. Automated failover keeps every location running when primary connections fail.
Risk-directed compliance.
Always audit-ready.
Continuous PCI DSS compliance monitoring, vulnerability management, and penetration testing on a unified platform. Backed by 100+ Qualified Security Assesors (QSAs) on staff in 16 countries.
Scale without friction.
From 10 to 10,000 locations.
Open a new location or onboard a new franchisee in days, not months. The same technology stack is deployed the same way, every time.
.avif)

Simply works. From HQ to your frontline.
One program. Built for the way distributed enterprises actually run.
For your company.
- One standard, enforced at every location. No drift. No gaps.
- Centralized visibility across hundreds or thousands of sites in the Asgard Platform.
- PCI DSS managed end-to-end by compliance experts on staff.
- One vendor relationship. One platform. One accountable partner.
- Brand protection. One weak location no longer puts the entire brand at risk.
For your locations.
- Plug-and-play setup. Equipment arrives configured. Locations stay focused on growing your business.
- 24x7 monitoring. Threats identified around the clock, even when locations are closed.
- Always-on connectivity. Broadband, 5G, and cellular failover keep every transaction flowing.
- Help when something breaks. A dedicated team responds, so site-level issues don't become brand-wide problems.
- No cybersecurity expertise needed on-site. Your teams keep your business running. We keep it protected.
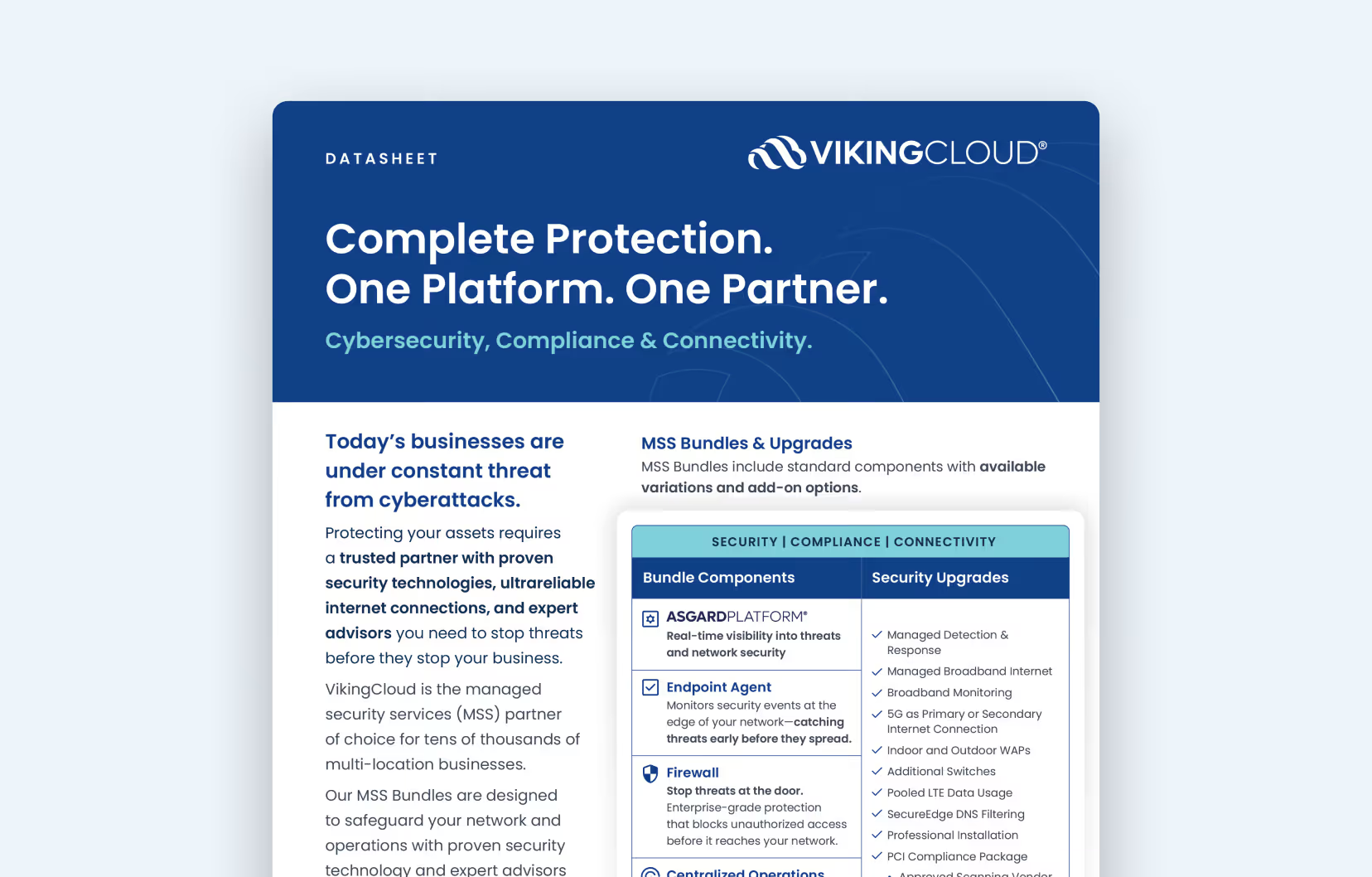
What’s included in VikingCloud’s comprehensive Managed Security Services?

Outsourced management of:
Security
Connectivity
Compliance
The Asgard Platform® to see it all
Security technology, internet access, and expert security and compliance teams to create a standard blueprint across all locations.
Real security that simply works. Zero shortcuts.
Know your real risks.
We have eyes on your assets 24x7 so you can focus on managing and growing your business. VikingCloud’s detection capabilities scale with your operations, whether you’re adding sites, deploying new technology, or expanding into new markets.
Technology for growing sites
- Network standardization and security blueprint
- Firewall configuration management
- Multi-Factor Authentication (MFA)
- Web filtering and DNS filtering
24x7 threat monitoring
- Security Information and Event Management (SIEM)
- Real-time alerting and customizable contact preferences
- Log management and retention
Vulnerability management
- Vulnerability Scanning
- Penetration Testing
Block attacks automatically.
Designed to stop threats before they stop business. Enterprise-grade protection that simply works—out of the box—at every location.
Get back to business fast.
Our global team of cybersecurity professionals and expert advisors are always on, and always ready for the most complex cybersecurity challenges. When something looks wrong, we investigate. When something is wrong, we intervene.
Managed Detection & Response (MDR)
NOW AVAILABLE: MDR Essentials
- 24x7 Security Operations Center with certified analysts
- Hands-on threat response—endpoint isolation, malicious process termination, and threat removal
- Threat hunting for hidden and emerging threats
- Root cause and impact analysis with hardening recommendations
Rapid incident containment & investigation
- Average time to containment: less than 30 minutes
- Containment to prevent lateral movement across your network
- Fully managed remediation
- Notifications in the Asgard Platform
Compliance made easy
- 24x7 security analyst and technical support
- PCI DSS continuous compliance management and reporting
- Self-Assessment Questionnaire (SAQ) wizard and population
- PCI DSS security awareness training
- Approved Scanning Vendor (ASV) services
- 24x7x365 security analyst and technical support
Know your real risks.
We have eyes on your assets 24x7 so you can focus on managing and growing your business. VikingCloud’s detection capabilities scale with your operations, whether you’re adding sites, deploying new technology, or expanding into new markets.
Technology for growing sites
- Network standardization and security blueprint
- Firewall configuration management
- Multi-Factor Authentication (MFA)
- Web filtering and DNS filtering
24x7 threat monitoring
- Security Information and Event Management (SIEM)
- Real-time alerting and customizable contact preferences
- Log management and retention
Vulnerability management
- Vulnerability Scanning
- Penetration Testing
Block attacks automatically.
Designed to stop threats before they stop business. Enterprise-grade protection that simply works—out of the box—at every location.
Get back to business fast.
Our global team of cybersecurity professionals and expert advisors are always on, and always ready for the most complex cybersecurity challenges. When something looks wrong, we investigate. When something is wrong, we intervene.
Managed Detection & Response (MDR)
NOW AVAILABLE: MDR Essentials
- 24x7 Security Operations Center with certified analysts
- Hands-on threat response—endpoint isolation, malicious process termination, and threat removal
- Threat hunting for hidden and emerging threats
- Root cause and impact analysis with hardening recommendations
Rapid incident containment & investigation
- Average time to containment: less than 30 minutes
- Containment to prevent lateral movement across your network
- Fully managed remediation
- Notifications in the Asgard Platform
Compliance made easy
- 24x7 security analyst and technical support
- PCI DSS continuous compliance management and reporting
- Self-Assessment Questionnaire (SAQ) wizard and population
- PCI DSS security awareness training
- Approved Scanning Vendor (ASV) services
- 24x7x365 security analyst and technical support
Industries we serve.
Click an industry below to see how VikingCloud helps businesses build cybersecurity and compliance programs across HQ and remote sites, by protecting against threats, meeting regulations, and keeping business uninterrupted.
Case Studies
Read our case studies to find out how VikingCloud helps businesses across diverse industries to overcome cybersecurity and compliance challenges.
Our case studies showcase real-world success—where proactive protection meets seamless operations—keeping businesses secure, compliant, and uninterrupted.
Asgard Platform: One hub for cybersecurity, connectivity & compliance.
VikingCloud’s AI-powered Asgard Platform gives Managed Security Service customers a unified view of their entire security posture:
- Real-time threat management and alerting
- Continuous monitoring & asset tracking across all locations
- Interactive dashboards with Cyber Risk Scoring
- Internet continuity & failover insights
- Streamlined cybersecurity & compliance management
One platform. One partner. Validated at scale by many of the world's most trusted brands.
%201.png)
Datasheets
Get more details on VikingCloud’s suite of cybersecurity and compliance services.
Discover why millions of businesses choose VikingCloud.



.avif)
24x7 expert support. Anytime you need it.
VikingCloud’s expert global support team is always on, ready to assist with your security and compliance challenges, day or night. Whether you need technical support or help with critical incidents, we’re here to provide real-time solutions.
MSS FAQs
Here are common questions we are asked about our Managed Security Services. For additional terminology and information, check out our Cybersecurity Glossary.
What is a managed security service?
Managed security services involve outsourcing an organization's cybersecurity operations to specialized providers who monitor, detect, and respond to threats, ensuring robust protection of digital assets.
How much do managed security services cost?
The cost of managed security services varies based on the organization's size, specific security requirements, and the range of services provided. Engaging a Managed Security Service Provider (MSSP) can be more cost-effective than building an in-house security team or purchasing and maintaining security equipment and software.
MSSPs offer access to specialized expertise and advanced security technologies, allowing organizations to achieve robust protection without the significant expenses associated with developing these capabilities internally. By outsourcing security operations, businesses can efficiently allocate resources, ensuring comprehensive security measures are in place while adhering to budget constraints.
What services do managed security providers offer?
Services include 24x7 network monitoring, threat detection, incident response, vulnerability management, firewall management, and compliance reporting.
What are the benefits of using managed security services for my organization?
Benefits include access to specialized expertise, advanced threat detection technologies, cost efficiency, scalability, and enhanced compliance with security regulations.
They offer continuous threat monitoring, expert incident response, and help maintain compliance, allowing your organization to focus on core operations while ensuring security.
What challenges do managed security services address?
Organizations often face challenges such as staffing shortages, managing complex security infrastructures, and staying ahead of evolving cyber threats.
MSS providers offer specialized expertise, streamline security operations, and provide continuous threat monitoring to effectively mitigate these issues.
What is the difference between MSS and MSSP?
Managed Security Services (MSS) are the actual security functions provided, while a Managed Security Service Provider (MSSP) is the company delivering these services.
How do I choose a managed security services provider?
Consider factors like the provider's experience, range of services, technology used, customization capabilities, reputation, and alignment with your organization's security needs.
An MSSP acts as an extension of your security team, providing expertise, technology, and continuous monitoring to protect your organization from cyber threats.
What is Managed Detection & Response (MDR)?
MDR is a 24x7 security service that combines elite cybersecurity analysts with advanced threat detection technology. MDR allows businesses to extend their security operations without the cost and complexity of building and maintaining an in-house Security Operations Center (SOC).
VikingCloud News & Resources
Check out the latest news and resources from VikingCloud.













.png)