Item Count :
00
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.

Consulting Team Spotlight: Michael Aminzade

Penetration Testing Examples: Real-World Scenarios & Insights

The Human Element in Risk-Based Security: Building a Culture of Cyber Resilience

Retail Cybersecurity Stats, Threats, and Solutions for 2026
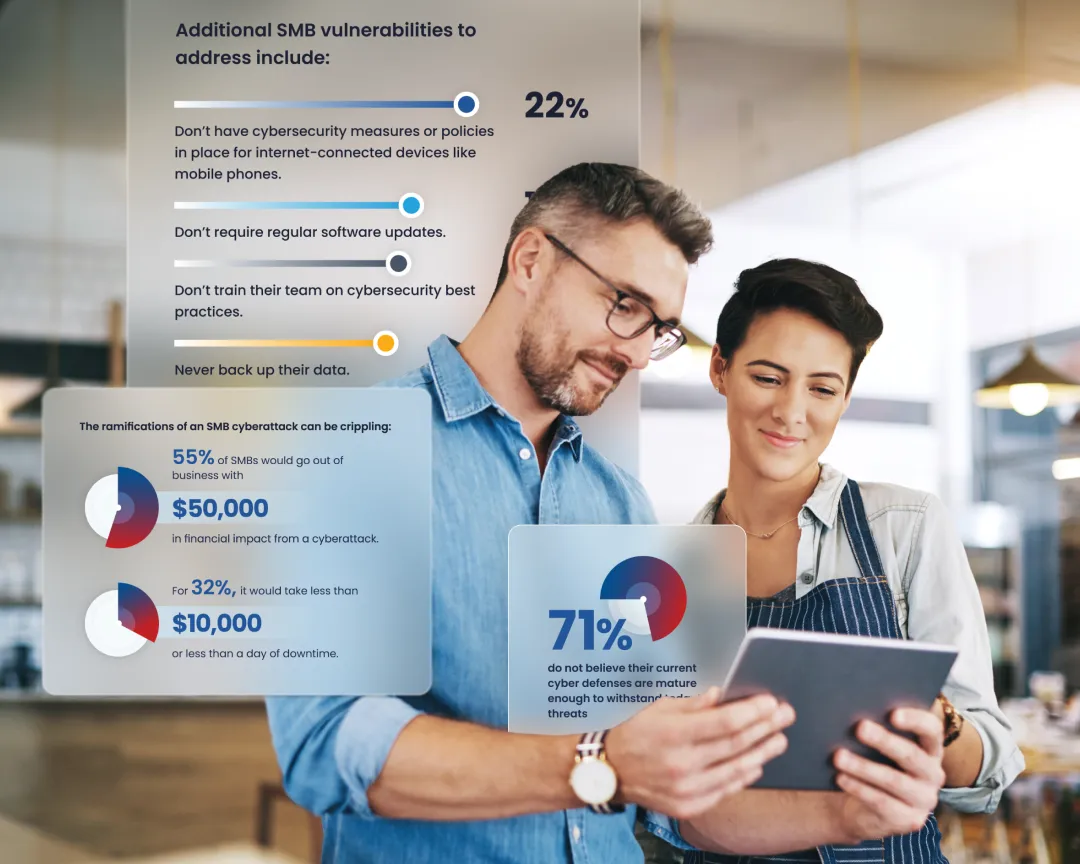
SMB Cybersecurity Survey Statistics and Threats

The Biggest Cyber Attacks in History

Final Countdown to Compliance: Preparing for PCI DSS v4.x

What is Penetration Testing as a Service (PTaaS)?

Risk-Based vs. Compliance-Based Security: Why One Size Doesn’t Fit All

Consulting Team Spotlight: Keaton Lane
.webp)
205 Cybersecurity Stats and Facts for 2026

Penetration Testing vs Vulnerability Scanning: Key Differences

Physical Penetration Testing: A Complete Overview

PCI 4.0 Authenticated Scanning — Go Live

7 Penetration Testing Tools Every Professional Should Know

Web Application Penetration Testing: Key Insights for Security

Compliance Team Spotlight: Brian Odian

DAST vs Penetration Testing: Understanding the Difference

Cybersecurity 2025: Lessons Learned & Expected Trends

Why Penetration Testing is Important

A Target in Every Room: Why Cybercriminals Are Hunting Small Hospitality Businesses and How to Protect Yours

What is Infrastructure Penetration Testing?

What is the Penetration Testing Execution Standard (PTES)?

What is Penetration Testing?

Guide to Gray Box Penetration Testing